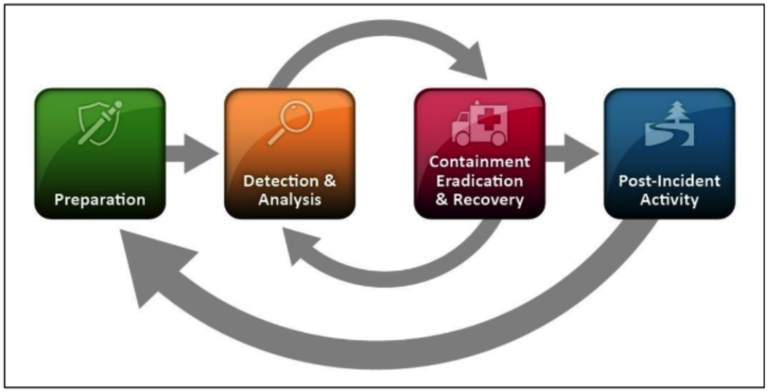
Stages of Incident Response
Stages
When talking incident response, the standard process that is followed in handling an incident is outlined by the following stages:
 Preparation
Preparation- Identification
- Containment
- Eradication
- Recovery
Preparation is not only the first phase but the most crucial phase. Preparation determines the effectiveness of your incident response capabilities. In practice, the essence of preparation is woven throughout the entire process. Preparation is also the phase where implicit critical functions of effective incident handling are explicitly stated. Proper preparation will dictate the maturity of your incident response team and the business impact can be quantifiably measured.
The focal points of preparation are:
- Policy
- Communication
- Tools
- Training
- Responsibilities
Policy
In order for an incident response plan to be effective, the very first step is to obtain backing from the top of the organization. This backing will ensure that the organization as a whole will support the incident response plan and provide the necessary time and resources to maximize its ability to be successful. Executive support initially manifests itself in the form of policy that is signed off by the organization’s leadership. A good policy protects the mission of the incident response team by giving it the necessary authority to accomplish it. The policy provides a written set of principles, rules, or practices that dictates how the organization will respond to an incident.
Defining the policy can be a daunting process due to there being many realms of information security that could be impacted by an incident. Acceptable use, employee termination, data archival, access control, and password management are just a small sample of how the tentacles of incident response may spread. The policy can impact multiple departments that may have competing needs due to their own individual mandates. Creating an overarching policy that that meets legal, regulatory, and operational requirements may take a significant investment in time and resources. But, it is a necessary step in order to understand how the entire organization functions to help facilitate implementing an effective incident response team.
Responsibilities
The process of creating a policy begins to draw into focus the different roles that will be needed to support the incident response process. Traditional incident roles such as a security manager or analyst tend to be clear. Cross-functional support from other departments is integral to the success of the team’s ability to remediate incidents. These departments navigate the ramifications of the incident around legal, compliance, and public relations concerns.
The identified roles should have their responsibility explicitly defined for the incident response process. The roles will have different responsibilities depending on which phase of the incident response process the organization is currently executing.

Communication
The analysis conducted throughout policy development helps facilitate the defining of communication channels and processes that should occur during an incident. One of the common missteps during development of an incident response plan is neglecting to identify a key stakeholder in the handling of an incident.
Laws and regulations may dictate the outside entities that your organization must communicate with in the event of an incident. The communication plan should identify those entities and define the procedures of notification. Special attention should be paid to vendors, customers, and service providers when developing a plan.
The communication plan should also set clear guidelines for when to involve law enforcement and who will coordinate between the organization and agencies. The primary reason why a security incident does not lead to criminal charges is that the organization did not handle the incident and communication with law enforcement correctly. The person(s) designated as the lead contact should communicate with law enforcement in a clear and consistent manner that corresponds to the procedures defined by the organization and law enforcement.
Tools
A key component of the policy creation process is defining the capabilities of the incident response team. Clearly defining the responsibilities of your incident response team is integral to setting the organization up for success. Some services may be handled internally while others may be outsourced. The tools that are implemented are designed to be in-line with defined capabilities.
Each phase of the incident response plan will have tools associated with it. The detection and analysis phase will have tools to streamline incident reporting, capture network traffic, and conduct behavioral analysis. Incident containment and recovery phase will have tools to limit network/system access and facilitate restoration of services within the defined recovery time windows. Post-incident tools can be used to update the organization’s threat intelligence and knowledge base.
Training
Once the tools and procedures have been defined, all staff who are to be involved in the incident response process will need to be trained regularly. Training can take shape in many different forms. The key is to make the training relevant and encompassing of different scenarios. Tabletop exercises that involve all of the relevant departments is one of the most effective ways to fine tune the incident response process. A tabletop exercise is a simulated exercise where participants gather to discuss incident processes. It provides flexibility that is difficult to obtain with live exercises and is inclusive to all the roles within the organization. Tabletop exercises allow for the organization to identify gaps that may exist. They also allow an organization to apply the lessons learned in a controlled environment.
Regular practice allows for your company to perform at maximum efficiency during a live incident.
A popular Sun Tzu quote is “know yourself and you will win all battles.” Knowing yourself comes with extreme care being taken during the preparation phase and conducting deliberate practice to discover weaknesses. A mature and effective incident response team is not created via a canned technological solution or any other magic bullet. They are built with meticulous attention in preparing to execute the detection, containment, and post-incident activities.
Reference:
Computer Security Incident Handling Guide
